What Are Agent Guardrails
Agent guardrails are the checks and boundaries that keep an agent useful, safe, and within its intended operating scope.
This guide explains what agent guardrails are, how they work in practice, and why they matter once an agent can call tools or take actions. It focuses on operational boundaries rather than abstract safety language.
Related Tools
Details
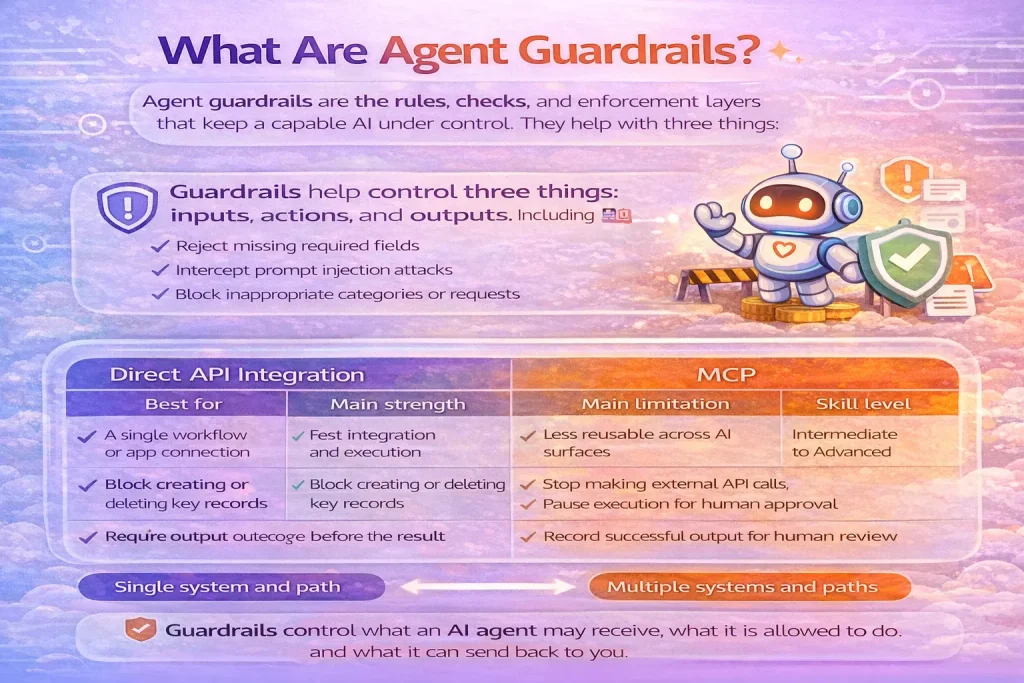
Agent guardrails are the rules, checks, and enforcement layers that keep an AI agent inside acceptable behavior. In practice, they decide what the agent is allowed to do, what it must validate before acting, when it needs human approval, and when a run should stop or fail.
They matter because an agent is not just generating text. Once it can call tools, fetch records, send messages, update tickets, or trigger workflows, weak boundaries become an operational problem rather than a prompt problem.
What agent guardrails do
Guardrails help control three things: inputs, actions, and outputs. Input guardrails screen what the agent receives. Action guardrails restrict which tools can be called and under what conditions. Output guardrails check whether the final response or next action is acceptable before it leaves the system.
For example, a CRM agent may be allowed to read contact data and draft updates, but not delete records. A support agent may be allowed to suggest refund actions, but only a human can approve the final refund. A research agent may browse documents freely, but must produce structured output that passes schema validation before the result is stored.
How guardrails work in practice
- Input validation: reject malformed requests, unsafe prompts, or missing required fields.
- Permission boundaries: limit each tool to read-only, write, or approval-required use.
- Schema checks: enforce output structure before the result reaches a downstream system.
- Approval checkpoints: pause for a person before high-risk actions.
- Stopping conditions: end runs after a fixed number of iterations or repeated failures.
- Policy checks: block restricted categories of actions such as sending external emails or changing billing records.
Who should care about them
Any team building agents that access business systems should care about guardrails. They are especially important in customer support, internal operations, finance, HR, legal workflows, and any system that can touch records, approvals, or external communication.
If your system only summarizes one document for internal review, guardrails can be lighter. If your system can change state in another system, they should be much stronger.
How guardrails differ from prompts
A prompt tells the agent what it should try to do. A guardrail determines what the system will actually allow. That distinction matters because prompts are advisory; guardrails are enforceable.
Relying on instructions alone is rarely enough once tools are involved. For example, “do not send external emails without approval” is a weak guarantee if the system still exposes the send-email tool without a hard approval gate.
Common types of guardrails
| Guardrail type | What it protects | Example |
|---|---|---|
| Input guardrail | Bad or unsafe requests | Reject missing account IDs |
| Tool guardrail | Unsafe or excessive actions | Allow read-only database search |
| Output guardrail | Invalid responses | Require JSON schema before storage |
| Approval guardrail | High-risk actions | Human must approve record changes |
| Run guardrail | Unbounded loops | Stop after five failed tool attempts |
When guardrails are not enough on their own
Guardrails do not replace evaluation, logging, or monitoring. They reduce risk, but they do not tell you whether the agent chose the best plan or whether the result was genuinely useful. That is where traces, tests, and human review still matter.
When templates help
A template can help with the outer workflow: capturing approval responses, routing results to Slack, saving validated outputs to Airtable, or creating review queues. What it usually does not solve by itself is policy design. You still need to decide which actions are allowed, who can approve them, and what should happen when a check fails.
FAQ
Are guardrails the same as moderation?
No. Moderation is one type of guardrail. Guardrails also include tool permissions, approval steps, schema validation, and stopping conditions.
Do simple agents need guardrails?
Yes, but the level should match the risk. Read-only internal summarization needs fewer controls than an agent that can edit records or contact customers.
Can guardrails slow down workflows?
Yes, especially when human approval is involved. That tradeoff is usually worth it for higher-risk actions.
Conclusion
Agent guardrails are what turn a capable model into an operable system. They define what the agent may do, what it must prove before acting, and when control must return to a human or a stricter workflow layer.